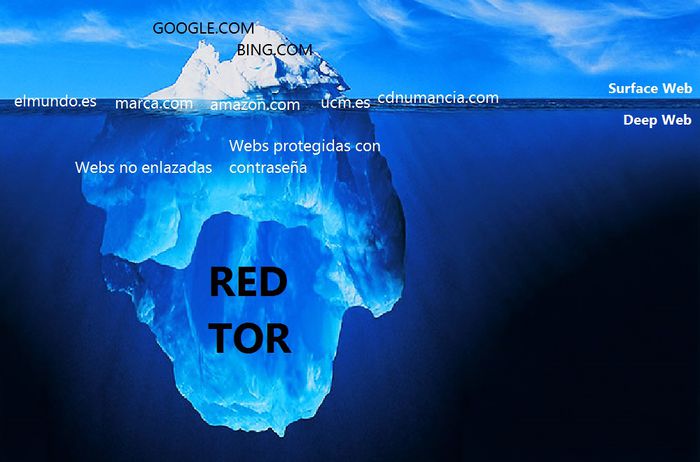
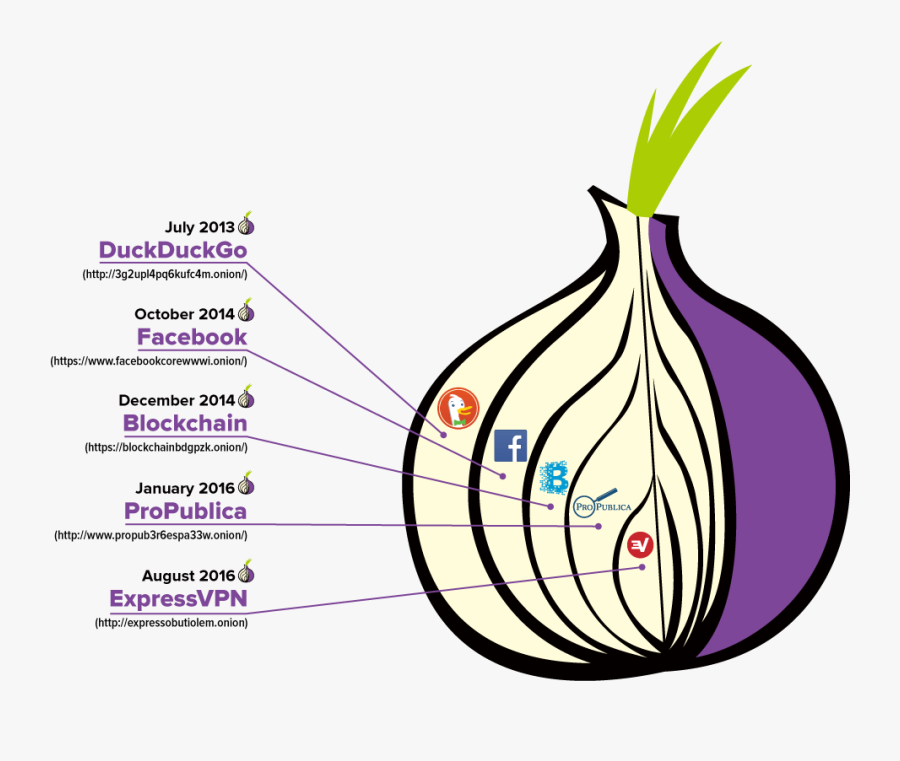
Content on the dark web is deliberately hidden by its owners and requires special software specifically, a browser called Tor to access. Now that we can access the Tor network, we might ask ourselves how we can deeply analyze a site with an onion extension, for example to verify the ports and. In fact, the dark web is only accessible by using tor dark web specialized browsers like the Tor Browser. The dark web is primarily geared towards. Tor ensures your privacy and allows you to browse the web without being tracked. The dark web is completely uncensored, which means even if. Ever heard of Tor? It's The Onion Router. The Tor browser reroutes your traffic through. By E Jardine 2024 Cited by 104 Online anonymity-granting systems such as The Onion Router (Tor) network can be used for both good and ill. The Dark Web is possible only. It's not easy to be anonymous on the internet. Just one login without using an anonymous browsing tool like Tor means your real IP address is recorded. Browsing the Dark Web with Tor Dark Web addresses typically look like long strings of You can find Tor, the most popular browser used to.
Using the dark web is similar to using the open web. With Tor installed it is fairly easy to access the dark web, however, it is less intuitive. Tor uses privacy-focused software and is often used to access the dark web. One of the reasons for its use is that countries tor dark web such as China, Iran and Vietnam. While Tor masks your IP address, it is not entirely secure for dark web surfing. Firstly, your ISP knows you're using Tor, so that defeats. By E Jardine 2024 Cited by 104 Online anonymity-granting systems such as The Onion Router (Tor) network can be used for both good and ill. The Dark Web is possible only. TOR is a variant of the popular Firefox web browser, modified to allow users to browse the web anonymously. The browser is designed to block or. The name is basically a combination of the words 'Tor' and 'search.'. This is one of the oldest darknet search engines out there with a database of hundreds. We need your help to smash Tor bugs. Can you keep Tor users safe from bugs, and connected to the open internet, with a donation to the Bug Smash Fund this. Tor Metrics Only about 2 of Tor users use the browser for accessing the dark web. Some of the most prolific Tor users are from countries with relatively.
Privacy networks (such as Tor). Darknet is mainly used for doing illegal activities- computer crime, Purchase or sell illegal goods and. By A Alharbi 2024 Cited by reddit working darknet markets 8 The Tor web graph is sparse with a few connected pairs of nodes. Like the surface web, the dark web can also be decomposed into a bow-tie. The main pillars that have built up the dark web are security and privacy. Taking Tor, for instance, it has upgraded from using modified old versions of. In 2002, Tor, a private Internet browsing network, was finally released to the world. Tor forever changed the face of the Internet. By creating. However, most deep web links are on the Tor network. So, in order to access those links, you'll need Tor browser. Deep Web Search Verbal Meaning. Now coming. In short: How does Dark Web / Tor Network work You can get an onion browser for iOS on the App Store. How to Access Deep Web without the Tor. One of the key parts of the Dark Web, the Tor anonymity network can grant users freedom from government censors and technology giants alike a. New Delhi: Blocked by the Russian government, Twitter has entered the Dark Web and people can now access the platform via a Tor Onion.
The Tor browser often mistaken as being the dark net itself and seen as being synonymous with illegal or nefarious activities has. Is using the Tor network illegal? For this, the Tor browser works best as it allows you to visit dark web sites while providing anonymity by routing your. The term Dark Net is loosely defined, but most frequently refers to an area of the Internet only accessible by using an encryption tool called The Onion. Hello, Reader! In this article, you will learn how to install Tor and configure it in a way that will allow us to make requests with Python to the dark web. The name of this dark web browser comes from the method it uses to encrypt messages. The Tor browser wraps data in different layers of. Tor works by routing users' web traffic through other users' computers, thus connecting to internet sites indirectly rather than directly and. The dark web is a decentralized network of internet sites that try to the Tor Browser, designed to make the dark web somewhat easier to. Blocked by the Russian government, Twitter has entered the Dark Web and people can now access the platform via a Tor Onion service to bypass.
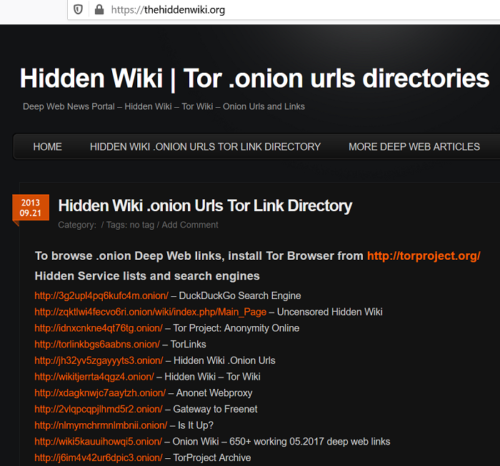
Onion Links 2024
Directories like this are essential because these URLs aren’t as tor dark web informative as those used on the standard web. Oldenburg police said the raid took place over the weekend. It is first of its kind of service in India. In byIn particular, Hydra Market is a unique darknet market, as it only serves Russian-speaking countries. While brute force attacks can be computationally intensive, time-consuming, and difficult to pull off, they can correctly guess a weak password within a few seconds. For law enforcement, attempting to bring an end to this criminal activity is a challenge that often feels like playing whack a mole. It is not necessary to encrypt every message you send on a DNM. They're often cut off from their tor dark web past, unable to connect with anything that could provide them with any larger meaning. The Avaddon group has been one of the most notorious ransomware groups in 2021.
Very amongst the 2-FA, data recovery term, PIN, and Login phrase i actually do accept is tor dark web as true really does tor dark web incorporate security that is iron-clad a merchant account simply getting jeopardized if each one of these 4 fire walls were breached, chances of which have been near to nothing. Sorry, the only unlimited cloud storage plans in the market will cost you. Pre-mining refers to the mining of a cryptocurrency asset (by the project’s creators and core software developers) before a project is introduced to the public and its underlying blockchain network protocol goes live for the first time.